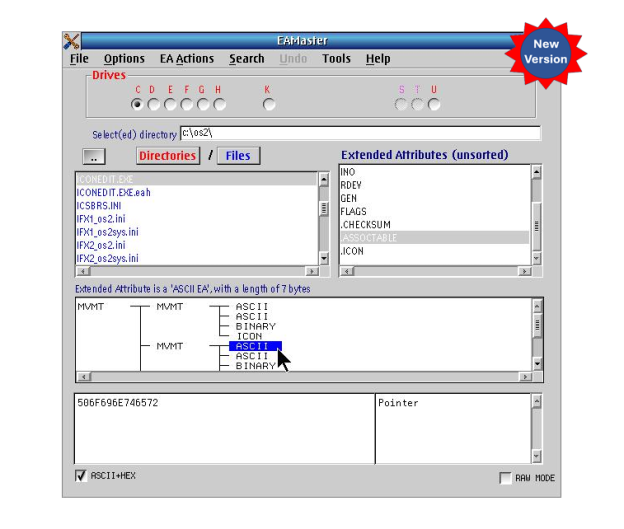
Following onto the October release of last year, Keith Merrington has again updated his handy EAMaster utility to v1.2.1. This latest build now includes three new tools:
- A tool to examine hold files produced by the EAUTIL OS/2 command or by EAMaster.
- A utility to search and optionally correct duplicate or incorrect long name.
- A utility to compare the EAs between directories.
If you already have a license for EAMaster, simply download the latest version (which should be available on Hobbes) and install to upgrade your current installation. Your existing registration will be recognized, and you’ll be good to go immediately.
If you don’t yet have a license, please visit our store for more information on this extremely useful package.